External resource onboarding — governed from day zero
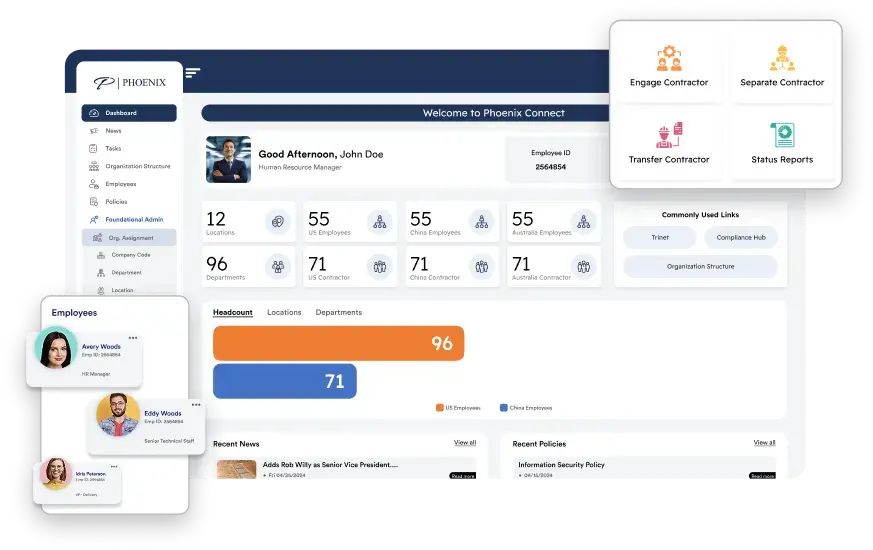
Every contractor, consultant, and vendor who touches your enterprise needs provisioned access, compliance clearance, and a governed exit. Phoenix Connect™ replaces fragmented onboarding with a single controlled pathway — from IT credentials and badge issuance to export control enforcement and automated offboarding.
The external workforce problem no one owns
Enterprises manage thousands of external resources across dozens of clients, programs, and facilities — yet onboarding remains a patchwork of emails, spreadsheets, and manual IT tickets. The result: compliance gaps, delayed start dates, orphaned access, and audit findings that could have been prevented.

One key. Every door.
IT credentials, physical badges, application entitlements, and compliance clearances — managed through a single provisioning engine instead of five disconnected workflows.
Role-based access profiles ensure every external resource gets exactly the access they need — nothing more, nothing less — with automatic revocation when contracts end.
End-to-end external workforce governance
Six integrated capabilities that replace fragmented onboarding with a single, auditable control plane.
External Resource Onboarding
Structured, repeatable onboarding for contractors, consultants, vendors, and acquisition roll-ins. Every external resource follows the same governed pathway into your enterprise — from day-zero paperwork to day-one productivity.
IT Access Provisioning
Automated provisioning of system credentials, VPN access, email accounts, SharePoint permissions, and application entitlements. Role-based access profiles ensure least-privilege compliance from the first login.
Physical Access & Badging
Badge issuance, building access configuration, secure zone clearance, and visitor management — integrated with enterprise badge systems, turnstiles, and biometric readers across every facility.
Secure Monitoring & Compliance
Real-time visibility into who has access to what, when they accessed it, and whether their clearance is still valid. Export control enforcement, ITAR/EAR compliance tracking, and automated access reviews.
Device & Endpoint Governance
Laptop provisioning, mobile device enrollment, endpoint security policy enforcement, and hardware asset tracking. Ensure every device meets your security baseline before connecting to corporate infrastructure.
Export Control & Data Classification
Automated export control screening, nationality-based access restrictions, data classification enforcement, and controlled technology access management for defense, aerospace, and regulated industries.
The governed onboarding lifecycle
From intake to offboarding — every step tracked, every access auditable, every compliance requirement enforced.
Intake & Clearance
Resource request initiated. Background checks, export control screening, NDA execution, and compliance verification run in parallel — not sequentially. Average intake reduced from 14 days to 48 hours.
Access Provisioning
Role-based access profiles automatically provision IT credentials, system entitlements, VPN access, email, SharePoint, and application permissions. Zero manual IT tickets for standard onboarding.
Physical Access & Badging
Badge creation, facility access configuration, secure zone clearance, and parking assignments coordinated across all locations. Visitor escort requirements and safety training tracked automatically.
Orientation & Compliance
Guided onboarding workflows deliver required training, policy acknowledgments, safety certifications, and compliance documentation. Progress tracked in real-time with automated reminders.
Active Monitoring
Continuous access review, clearance expiration tracking, contract end-date enforcement, and anomaly detection. Every access event logged for audit readiness.
Offboarding & Revocation
Automated access revocation across all systems — IT, physical, network — triggered by contract end, project completion, or compliance event. Full audit trail preserved for regulatory evidence.
Your business process. Our governance engine.
Every enterprise operates differently. Phoenix Connect™ adapts to your existing workflows — not the other way around.
Client-Specific Workflows
We customize onboarding, provisioning, and offboarding workflows to mirror your existing business processes — preserving institutional knowledge while adding governance and automation.
Global & Local Rules
Standardized process framework with configurable global and local rules, approval chains, and compliance steps that respect regional regulations, client policies, and facility-specific requirements.
100% Process Compliance
Every step is tracked, every rule enforced, every exception flagged. Real-time dashboards provide superior visibility into process adherence across all locations, clients, and resource types.
The result: A standardized, governed process engine that feels like it was built in-house — because it was configured around your rules, your approval chains, and your compliance requirements. No generic templates. No forced process changes.
Global Integration Ecosystem
200+ enterprise systems. One control plane.

Connects to the systems you already run
Phoenix Connect™ integrates with your existing IT, HR, physical security, and collaboration platforms — no rip-and-replace required.
IT Service Management
- ServiceNow
- Jira Service Management
- BMC Remedy
- Freshservice
- Ivanti
HRIS & HCM
- SAP SuccessFactors
- Workday
- Oracle HCM Cloud
- UKG Pro
- ADP
- Ceridian Dayforce
Identity & Access
- Azure Active Directory
- Okta
- Ping Identity
- CyberArk
- SailPoint
- ForgeRock
Physical Security & Badging
- Lenel OnGuard
- CCURE 9000
- Genetec
- Honeywell Pro-Watch
- HID Global
- S2 Security
ERP & Finance
- SAP S/4HANA
- Oracle Financials
- Microsoft Dynamics 365
- NetSuite
- Infor
Collaboration & Productivity
- Microsoft 365 / SharePoint
- Google Workspace
- Slack Enterprise
- Confluence
- Teams
Built for regulated enterprises
Defense, aerospace, energy, financial services, and healthcare organizations trust Phoenix Connect™ to enforce access governance at scale.

- Least-privilege access enforcement across all systems and facilities
- Automated export control screening (ITAR, EAR, OFAC) at intake
- Real-time clearance expiration monitoring and access revocation
- Complete audit trail for every access grant, modification, and revocation
- SOC 2 Type II certified onboarding infrastructure
- Data classification enforcement and controlled technology access
- Nationality-based access restrictions for regulated programs
- Integration with enterprise SIEM and security operations platforms
Where enterprises deploy Phoenix Connect™
Contractor & Vendor Onboarding
Staffing firms, consulting partners, and managed service providers onboard external resources into client environments with governed access, compliance tracking, and automated offboarding.
Acquisition Roll-Ins
Rapidly integrate acquired workforce populations into your IT ecosystem, physical security infrastructure, and compliance frameworks without disrupting ongoing operations.
Regulated Facility Access
Defense, energy, and pharmaceutical sites with ITAR, export control, or clean-room requirements manage access clearance, escort protocols, and zone restrictions through a single platform.
Audit & Compliance Evidence
Generate complete access audit trails, clearance verification reports, and compliance evidence packs for SOX, SOC 2, ITAR, and regulatory examinations — on demand.
See how Connect™ governs your external workforce
Share your onboarding challenge. We'll walk you through how Phoenix Connect™ replaces fragmented processes with a single, auditable control plane — tailored to your systems, your compliance requirements, and your operational scale.